Explore the vendor landscape across six enterprise data management markets — all in one place.
Discover why Informatica from Salesforce is named a Leader across the following:
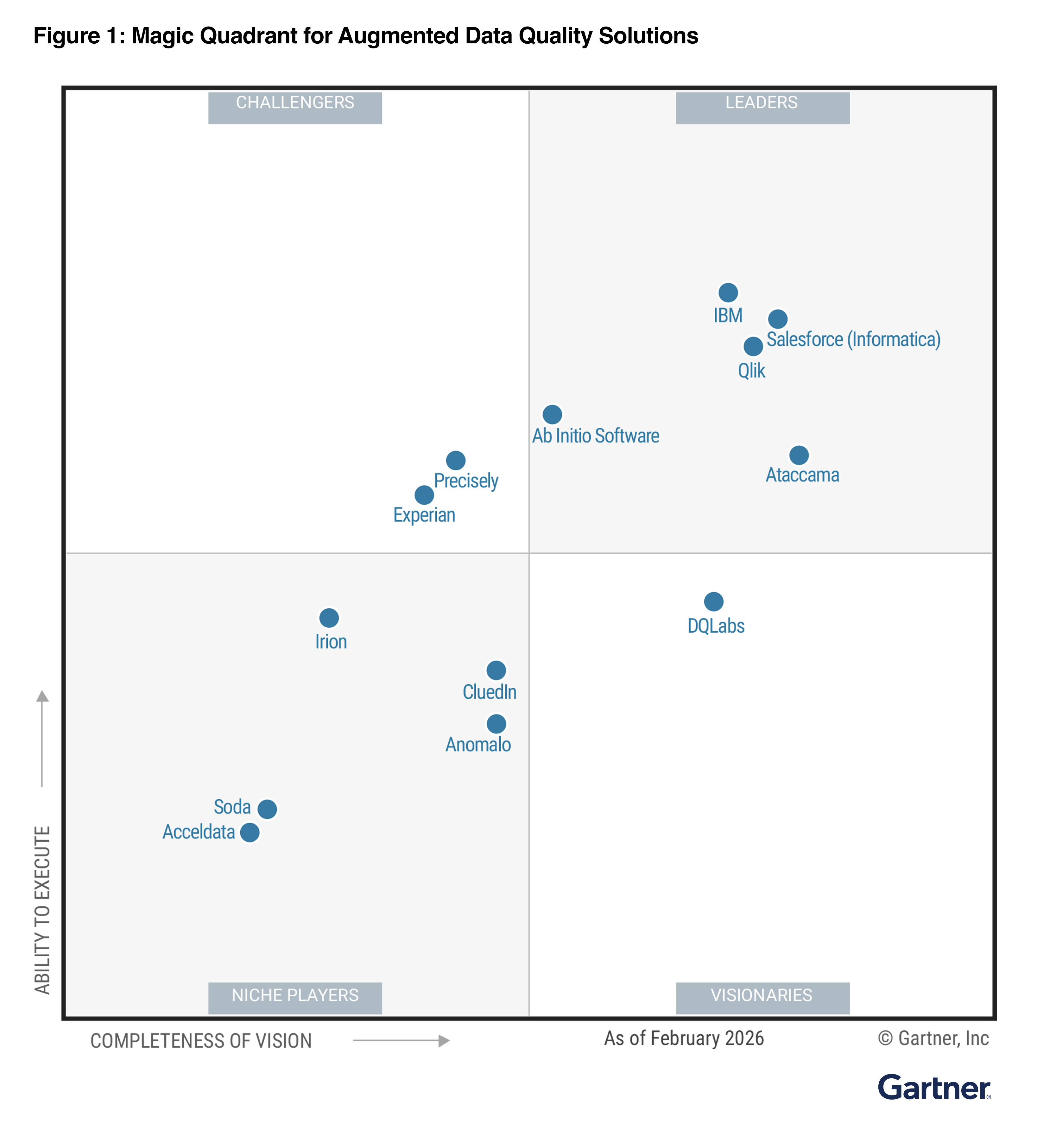
- Magic Quadrant™for Augmented Data Quality Solutions
- Magic Quadrant™ for Data and Analytics Governance Platforms
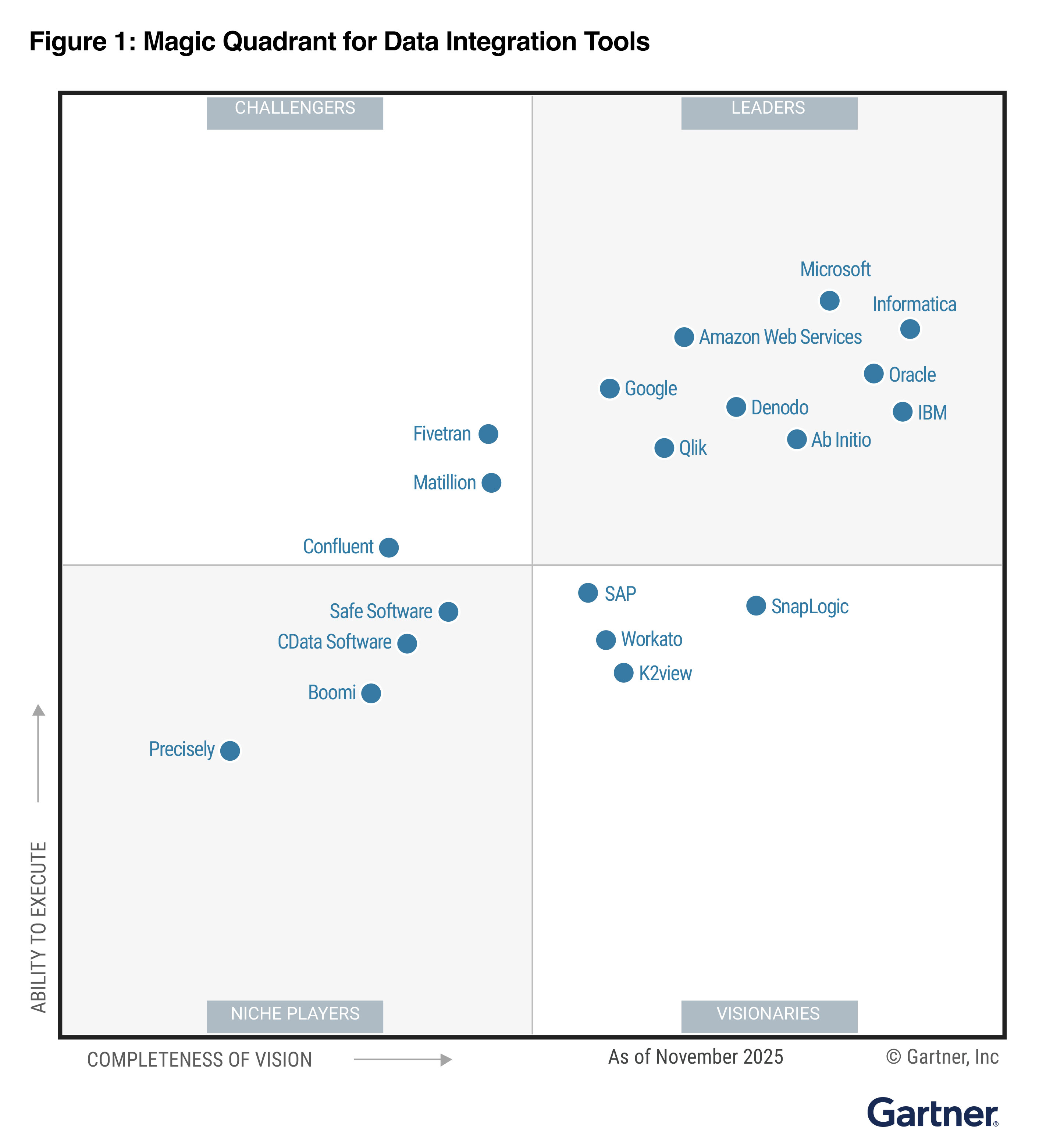
- Magic Quadrant™ for Data Integration Tools
- Magic Quadrant™ for iPaaS
- Magic Quadrant™ for MDM Solutions
- Magic Quadrant™ for Metadata Management Solutions
Magic Quadrant™ for Augmented
Data Quality Solutions1

Magic Quadrant™ for
Data and Analytics
Governance Platforms2

Magic Quadrant™ for
Data Integration Tools3

Magic Quadrant™ for
iPaaS4


Magic Quadrant™ for MDM Solutions5

Magic Quadrant™ for Metadata Management Solutions6

Here’s what you can expect from each report
1 Gartner Magic Quadrant for Augmented Data Quality Solutions, Sue Waite, Divya Radhakrishnan, Amy Bickel, 11 February 2026
2 Gartner Magic Quadrant for Data and Analytics Governance Platforms, Anurag Raj, Guido De Simoni, Sarah Turkaly, 6 January 2026
3 Gartner Magic Quadrant for Data Integration Tools, Michele Launi, Nina Showell, Robert Thanaraj, Sharat Menon, 8 December 2025
4 Gartner Magic Quadrant for Integration Platform as a Service, Andrew Humphreys, Keith Guttridge, Allan Wilkins, Shrey Pasricha, 16 March 2026
5 Gartner Magic Quadrant for Master Data Management Solutions, Stephen Kennedy, Lyn Robison, Divya Radhakrishnan, 6 April 2026
6 Gartner Magic Quadrant for Metadata Management Solutions, Melody Chien, Thornton Craig, Guido De Simoni, Roxane Edjlali, 19 November 2025
Gartner and Magic Quadrant are trademarks of Gartner, Inc. and/or its affiliates.
This graphic was published by Gartner, Inc. as part of a larger research document and should be evaluated in the context of the entire document. The Gartner document is available upon request from Informatica.
Gartner does not endorse any company, vendor, product or service depicted in its publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner publications consist of the opinions of Gartner’s business and technology insights organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this publication, including any warranties of merchantability or fitness for a particular purpose.